Confidential Computing: An In-Depth Resource on Safeguarding Data-in-Use in Today’s Digital Environment
Introduction
As organizations generate and process unprecedented volumes of data, protecting sensitive information has become a top priority in the digital age. Traditional security measures have effectively safeguarded data while it is stored (data at rest) and while it is being transferred across networks (data in transit). However, a critical vulnerability persists: the state when data is being processed — known as data-in-use.
Confidential Computing has emerged as a remarkable advancement in cybersecurity that addresses this gap by enabling encrypted data processing. Using hardware-based isolation techniques, ensures that data remains secure even while applications operate on it. This comprehensive guide explores what is, why it is essential, how it works, its real-world applications, challenges, and future prospects — equipping you with expert understanding of this powerful security paradigm.
Table of Contents
What Is Confidential Computing?
Confidential Computing is a security framework designed to protect data during active computation. In contrast with traditional security models that focus on data at rest and data in transit, Confidential Computing uniquely protects data in use, which has historically been vulnerable to attack.
This is achieved through hardware-based safeguards that create trusted execution environments — secure enclaves where sensitive data can be processed without exposure to the host system or external actors. Whether deployed in cloud environments, on local servers, or across hybrid setups, Confidential Computing enables organizations to handle sensitive workloads with enhanced privacy and trust.
The Importance of Data-in-Use Protection
Before Confidential Computing was widely adopted, data in use was often left unprotected in plain memory space while applications processed it. This created opportunities for:
- Malicious insiders to extract data
- Compromised operating systems to access sensitive information
- Cloud administrators to view or manipulate in-memory data
- Attackers exploiting memory vulnerabilities to steal or modify data
Confidential Computing closes this gap by ensuring that data remains encrypted and isolated, even within the system’s own memory. This development is particularly valuable in an era where cloud computing, multi-tenant environments, and third-party service providers are ubiquitous.
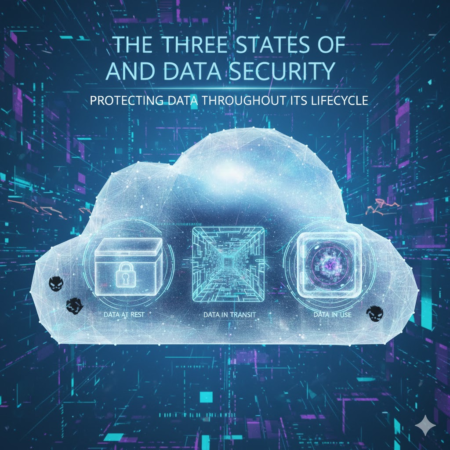
The Three States of Data Security
To appreciate the value of Confidential Computing, it’s important to understand the three states in which data exists and how security has traditionally been applied:
| State of Data | Protection Method | Security Status |
|---|---|---|
| Data at Rest | Encryption on disk or storage | Strongly protected |
| Data in Transit | Encryption during network transfer | Strongly protected |
| Data in Use | Traditionally vulnerable in memory | Newly protected by Confidential Computing |
While data at rest and in transit have been well secured with encryption protocols such as AES and TLS, data in use has remained exposed — until the emergence of Confidential Computing.
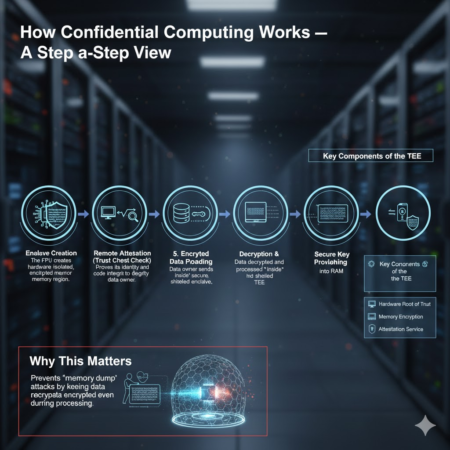
Trusted Execution Environments (TEEs)
At the core of Confidential Computing lies the concept of the Trusted Execution Environment (TEE). A TEE is a secure, isolated area within a processor that ensures data and code inside it are protected against unauthorized access or tampering.
TEEs provide:
- Hardware-based isolation: The data and code running inside the environment are inaccessible to the rest of the system.
- Integrity assurance: Only verified code can execute in the enclave.
- Confidentiality: Sensitive computations remain private, even from privileged system software.
Examples of TEE technologies include:
- Intel Software Guard Extensions (SGX)
- AMD Secure Encrypted Virtualization (SEV) and SEV-SNP
- ARM TrustZone
These technologies leverage advanced hardware features to create secure enclaves where sensitive operations can safely occur.

How Confidential Computing Works — A Step-by-Step View
Here is a simplified breakdown of how Confidential Computing ensures secure data processing:
- Data Encryption Before Processing
Sensitive data remains encrypted before it enters memory for processing. - Protected Execution inside TEEs
Data is decrypted only inside secure enclaves protected by hardware, ensuring that it is never exposed to the operating system or hypervisor. - Secured Key Management
Encryption keys are managed within secure hardware boundaries and never exposed outside trusted environments. - Execution and Isolation
Computation occurs within the TEE, isolated from other processes and system software. - Secure Output Encryption
Results from computation are encrypted before leaving the enclave, ensuring protection even after processing completes.
This workflow eliminates traditional security gaps and enables highly confidential computing tasks to be executed safely.
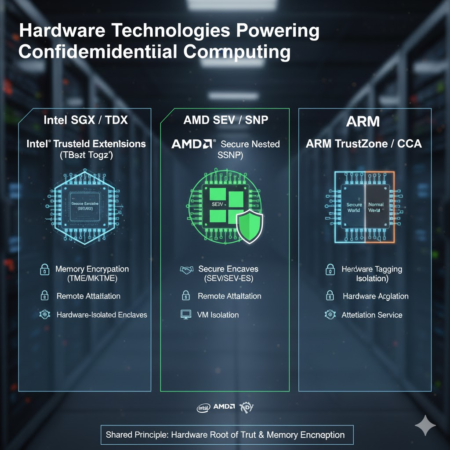
Hardware Technologies Powering Confidential Computing
IT relies on specialized hardware features in modern processors. Three of the most prominent implementations are:
1. Intel SGX (Software Guard Extensions)
Intel SGX enables the creation of secure memory enclaves, where data and code are protected from external access. SGX remains widely utilized for sensitive compute tasks such as cryptographic operations and secure analytics.
2. AMD SEV and SEV-SNP
AMD’s Secure Encrypted Virtualization encrypts the memory of virtual machines, enabling multiple tenants to run securely on shared infrastructure without exposing data to other VMs or the hypervisor.
3. ARM TrustZone
Commonly used in mobile and embedded systems, ARM TrustZone creates two execution worlds — secure and non-secure — providing hardware isolation for sensitive operations in resource-constrained environments.
Each of these technologies serves different deployment needs but shares the common goal of protecting data during processing.
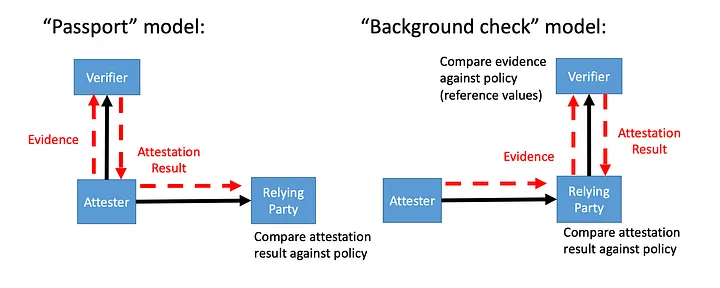
Remote Attestation: Building Trust Across Systems
Remote attestation is a critical feature of Confidential Computing. It enables one system to verify that code is running within a trusted enclave on another system. This verification is essential when workloads are outsourced to cloud environments or third-party infrastructure.
Remote attestation provides:
- Proof of authenticity and integrity of secure environments
- Assurance to data owners that computation is secure
- Trust without revealing sensitive code or data
This capability is foundational for secure multi-party collaboration and confidential data processing in distributed systems.
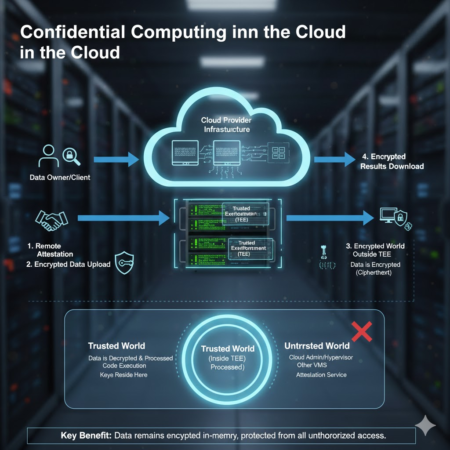
Confidential Computing in the Cloud
Cloud providers have integrated CC into their services, allowing customers to benefit from enhanced data protection in scalable, remote environments:
Microsoft Azure Confidential Computing
Azure enables secure processing with hardware-protected enclaves and confidential virtual machines (VMs), allowing sensitive workloads to run without exposing data to Microsoft or other actors.
Google Cloud Confidential VMs
Google Cloud’s solution offers encryption of data in use by running workloads in secure enclaves, seamlessly integrating into existing cloud workflows.
AWS Nitro Enclaves
AWS Nitro Enclaves provide isolated compute environments within EC2 instances, enabling secure data processing with minimal attack surface.
By integrating Confidential Computing into the cloud ecosystem, these providers empower organizations to leverage powerful
infrastructure without sacrificing data privacy and trust.
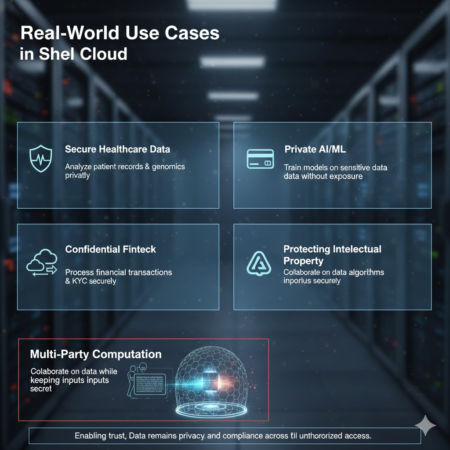
Real-World Use Cases
Confidential Computing has emerged as a transformative technology capable of securing a wide range of applications:
Healthcare
Hospitals and research organizations can process sensitive patient data — such as genomic records or clinical trial information — without risking exposure, enabling secure AI-driven analysis and medical research.
Financial Services
Banks and financial institutions can conduct fraud detection, risk modeling, and transaction processing in secure environments that protect customer data from unauthorized access.
Artificial Intelligence and Machine Learning
AI models often require training on sensitive datasets, such as medical images or private customer information. It enables secure model training without exposing raw data.
Government and Defense
Government bodies can leverage Confidential Computing to protect classified information, citizen data, and national security workloads from internal and external threats.
Multi-Party Collaboration
Multiple organizations can collaborate on shared data analysis — for research or business intelligence — while keeping their data secure from one another.
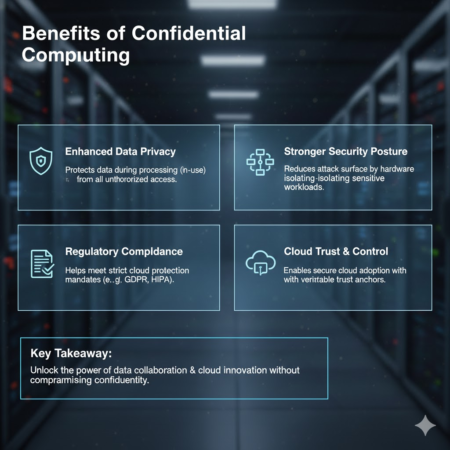
Benefits of Confidential Computing
Confidential Computing provides significant advantages in modern digital environments:
- Enhanced Data Security: Protects data throughout its lifecycle, including during computation.
- Insider Threat Protection: Prevents even privileged system users from accessing sensitive information.
- Cloud Trust: Increases confidence in cloud providers and third-party infrastructure.
- Compliance Support: Assists with regulatory requirements such as GDPR, HIPAA, and PCI-DSS.
- Secure Collaboration: Enables shared compute environments without risking data leakage.
These benefits position Confidential Computing as a foundational technology in secure computing architecture.
Challenges and Limitations
Despite its promise, Confidential Computing faces several challenges:
- Performance Overhead: Encryption and secure isolation can introduce computational overhead.
- Complex Development: Building applications for secure enclaves requires specialized knowledge.
- Hardware Dependency: Not all devices and environments support necessary hardware features.
- Debugging Difficulties: Traditional debugging tools may not function within secure enclaves.
Ongoing research and improvements continue to mitigate these challenges and broaden adoption.
Career Opportunities and Skills
Demand for professionals with expertise in Confidential Computing and cybersecurity is on the rise. Key roles include:
- Confidential Computing Engineer
- Cloud Security Architect
- Trusted Execution Environment Developer
- Cybersecurity Analyst
- Secure Systems Designer
Essential skills for these roles include:
- Cloud platforms (AWS, Azure, Google Cloud)
- Linux and virtualization
- Encryption fundamentals
- Hardware-based security understanding
- Secure code development
Salary Perspectives: Pakistan and the United States
Confidential Computing professionals enjoy competitive compensation worldwide.
In Pakistan
- Entry Level: PKR 80,000 – 150,000/month
- Mid Level: PKR 200,000 – 400,000/month
- Senior Level: PKR 600,000+/month
In the United States
- Entry Level: $90,000 – $120,000/year
- Mid Level: $130,000 – $160,000/year
- Senior Level: $180,000 – $220,000+/year
The growing importance of cloud security and data privacy fuels demand for this skill set, offering strong career growth and remote opportunities.
The Future of Confidential Computing
As digital ecosystems evolve with advanced technologies such as artificial intelligence, secure data marketplaces, and zero-trust architectures, Confidential Computing will play an increasingly vital role. Organizations will adopt these methods as standard practice for secure processing, enabling:
- Industry-wide trust in shared compute environments
- Secure global collaboration
- More robust compliance with emerging privacy legislation
Confidential Computing is no longer a niche technology — it is becoming essential for secure digital transformation.

Conclusion
Confidential Computing represents a major leap forward in cybersecurity by protecting data during its most vulnerable phase — while it is being used. Through hardware-enforced trusted execution environments, this technology ensures that sensitive information remains confidential, private, and secure even in shared infrastructure.
As cloud computing, AI, and data collaboration continue to shape the digital landscape, Confidential Computing will play a defining role in building trust, safeguarding privacy, and enabling powerful new applications. This comprehensive guide equips you with the knowledge and context needed to understand, apply, and advance in this critical field.
You may also like
________________
Businesses and Environmental Sustainability in Pakistan: Protecting Nature in 2026


